Abstract
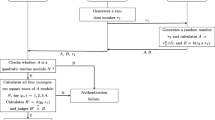
One of the key problems in radio frequency identification (RFID) is security and privacy. Many RFID authentication protocols have been proposed to preserve security and privacy of the system. Nevertheless, most of these protocols are analyzed and it is shown that they cannot provide security against some RFID attacks. Strong authentication and strong integrity (SASI) is the first ultra-lightweight authentication protocol introduced rotation shift operation and RFID authentication protocol with permutation (RAPP) is a new ultra-lightweight authentication protocol with permutation. In this paper, we give the security analysis on these two protocols. An active attack is presented on RAPP, and using the property of the left rotation and permutation operations, we can deduce the relationship of bits of random number or secret keys at different positions, thus obtain all the secrets shared by the reader and the tag. A passive full-disclosure attack is proposed on SASI. Using SASI’s construction weakness, our attack can reveal all the secrets shared by the reader and tag by eavesdropping about 48 rounds of the authentication messages.
Similar content being viewed by others
References
Hunt VD, Puglia A, Puglia M (2007) RFID: A Guide to Radio Frequency Identification. Wiley-Inter science
Vajda I, Buttyan, L (2003) Lightweight authentication protocols for low-cost RFID tags. In: the Second Workshop on Security in Ubiquitous Computing. Seattle, Washington
Juels A (2005) Minimalist Cryptography for Low-Cost RFID Tags (Extended Abstract). In: Fourth Conference on Security in Communication Network. Amalfi
Peris-Lopez P, Hernandez-Castro JC, Tapiador JME, Ribagorda A (2006) LMAP: a real lightweight mutual authentication protocol for low-cost RFID tags. In: Workshop on RFID Security 2006. Graz, Austria
Peris-Lopez P, Hernandez-Castro JC, Tapiador JME, Ribagorda A (2006) M2AP: a minimalist mutual-authentication protocol for lowcost RFID tags. In: 2006 International Conference on Ubiquitous Intelligence and Computing. Wuhan, China
Li T, Wang G (2007) Security analysis of two ultra-lightweight RFID authentication protocols. In: 22nd International Information Security Conference. Sandton, South Africa
Sadighian A, Jalili R (2009) AFMAP: Anonymous forward-secure mutual authentication protocols for RFID systems. Third IEEE International Conference on Emerging Security Information, Systems and Technologies, Athens, Glyfada
Sadighian A, Jalili R (2008) FLMAP: A fast lightweight mutual authentication protocol for RFID systems. In: 16th IEEE International Conference on Networks. New Delhi, India
Safkhani M, Naderi M, Bagher N (2010) Cryptanalysis of AFMAP. IEICE Electronics Express 7(17):1240–1245
Bárász M, Boros B, Ligeti P, Lója K, Nagy D (2007) Passive attack against the m2ap mutual authentication protocol for RFID tags. First International EURASIP Workshop on RFID Technology, Vienna, Austria
Chien HY (2007) SASI: A new ultralightweight RFID authentication protocol providing strong authentication and strong integrity. IEEE Transactions on Dependable and Secure Computing 4(4):337–340
Cao T, Bertino E, Lei H (2009) Security analysis of the SASI protocol. IEEE Transactions on Dependable and Secure Computing 6(1):73–77
Phan RCW (2009) Cryptanalysis of a new ultralightweight RFID authentication protocol—SASI. IEEE Transactions on Dependable and Secure Computing 6(4):316–320
Sun HM, Ting WC, Wang KH (2011) On the security of Chien’s ultralightweight RFID authentication protocol. IEEE Transactions on Dependable and Secure Computing 8(2):315–317
D’Arco P, De Santis A (2011) On ultralightweight RFID authentication protocols. IEEE Transactions on Dependable and Secure Computing 8(4):548–563
Avoine G, Carpent X, Martin B (2010) Strong authentication and strong integrity (SASI) is not that strong. In: Workshop on RFID Security—RFIDSec'10. Istanbul
Peris-Lopez P, Hernandez-Castro JC, Tapiador JME, Ribagorda A (2008) Advances in ultralightweight cryptography for low-cost RFID tags: Gossamer protocol. In: 9th International Workshop on Information Security Applications. Jeju Island, Korea
Tian Y, Chen G, Li J (2012) A new ultralightweight RFID authentication protocol with permutation. IEEE Commun Lett 16(5):702–705
Yeh KH, Lo NW, Winata E (2010) An efficient ultralight weight authentication protocol for RFID systems. In: Workshop on RFID security—RFIDSec Asia’10. Singapore
Li T (2008) Employing lightweight primitives on low-cost RFID tags for authentication. Vehicular Technology Conference, Calgary, Alberta
Bogdanov A, Knudsen LR, Leander G, Paar C, Poschmann A, Robshaw MJB, Seurin Y, Vikkelsoe C (2007) Present: an ultra-lightweight block cipher. Workshop on Cryptographic Hardware and Embedded Systems, Vienna, Austria
De Cannière C, Dunkelman O, Knežević M (2009) KATAN and KTANTAN—A family of small and efficient hardware-oriented block ciphers. Workshop on Cryptographic Hardware and Embedded Systems, Lausanne, Switzerland
Ojha SK, Kumar N, Jain K, Sangeeta L (2009) TWIS—a lightweight block cipher. Fifth International Conference on Information Systems Security, Kolkata, India
Aumasson JP, Henzen L, Meier W, Naya-Plasencia M (2010) QUARK: a lightweight hash. Workshop on Cryptographic Hardware and Embedded Systems, Santa Barbara, California
Acknowledgments
This work is supported by the Priority Academic Program Development of Jiangsu Higher Education Institutions (PAPD), National Natural Science Funds (Grant No.60903181) and Nanjing University of Post and Telecommunication Funds (Grant No. NY211064).
Author information
Authors and Affiliations
Corresponding author
Rights and permissions
About this article
Cite this article
Shao-hui, W., Zhijie, H., Sujuan, L. et al. Security analysis of two lightweight RFID authentication protocols. Ann. Telecommun. 69, 273–282 (2014). https://doi.org/10.1007/s12243-013-0361-z
Received:
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s12243-013-0361-z